Fkstrcghtc is a term that sounds unusual at first, but the ideas connected to it are easy to understand once you break them down. In most discussions, it points to hidden digital dangers that are hard to spot until they have already caused harm. These dangers often involve weak protection, risky data handling, silent system abuse, and security gaps that stay unnoticed in the background. For everyday users, businesses, and online services, the main concern is not just one attack but a chain of quiet problems that can grow over time. That is why this subject matters. It helps explain how hidden digital threats work, why encryption risks are often misunderstood, and what people can do to reduce the damage before it spreads.
What Fkstrcghtc Means in a Cybersecurity Context
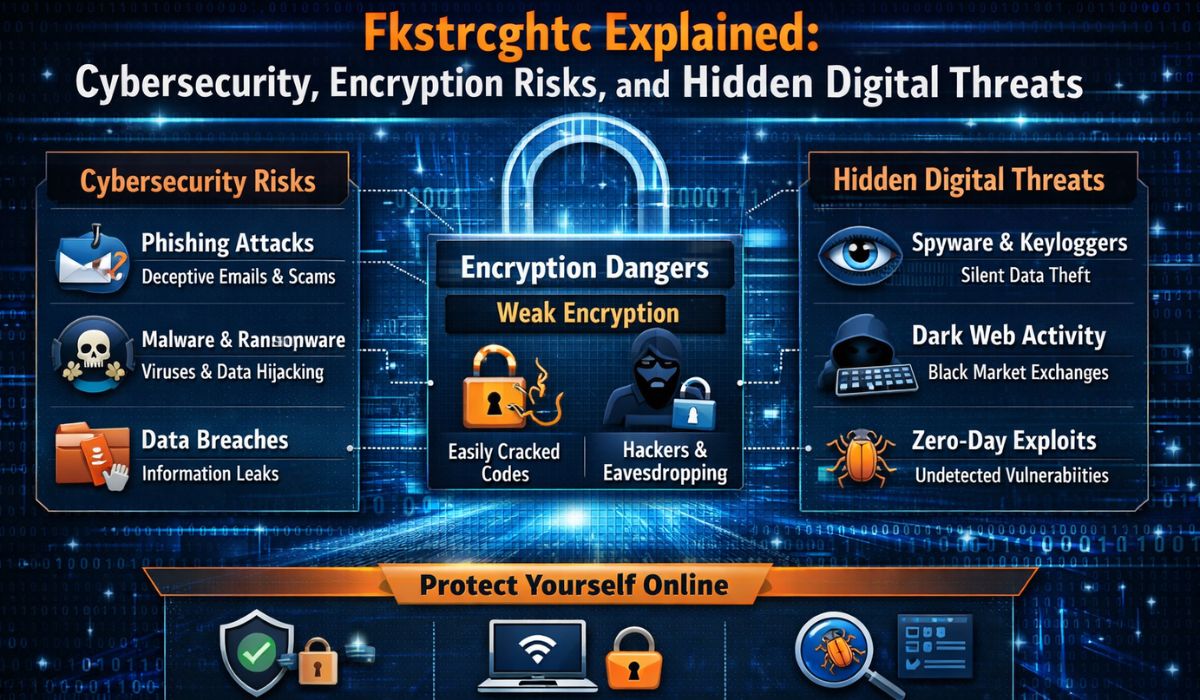
When people talk about this concept in a security setting, they are usually describing digital risk that hides behind normal system activity. It may not look like a dramatic hack on the surface. Instead, it can appear as small warning signs such as odd logins, strange file movement, weak password control, or software behavior that does not seem harmful right away. The danger grows because many security problems do not start with a loud event. They begin quietly, often through hidden access points, weak encryption practices, outdated tools, or poor user awareness. In simple terms, this idea helps describe the part of cyber risk that stays in the shadows while systems continue running as if everything is fine.
Why Hidden Threats Are So Dangerous
A hidden digital threat is dangerous because it often avoids attention for a long time. If a company notices a problem right away, it still has a chance to isolate the affected device, reset access, and protect customer data. But when the issue stays buried, attackers may study the network, copy information, change settings, or create backdoors for future use. The longer that goes on, the harder it becomes to know what was touched and what can still be trusted. This is why many security failures are not caused by one major mistake alone. They happen because small weaknesses build on each other until the risk becomes serious enough to affect privacy, operations, finances, and public trust.
ALSO READ THIS :- How Asalia Nazario Highlights Zoe Saldaña’s Impact in Film and Culture
The Role of Encryption and Where It Can Fail
Encryption is meant to protect information by making it unreadable to anyone without the right key. It is one of the strongest tools in digital safety, but it is not magic. Problems happen when encryption is used poorly, managed badly, or trusted too much without looking at the full system around it. For example, data may be encrypted while stored but exposed during transfer, or a secure file may still be stolen if the attacker gets access to the account that opens it. In other cases, old encryption methods become easier to break over time, especially if systems are not updated. This is where the concern becomes important. It reminds people that strong protection is not only about having encryption, but also about using it correctly, updating it often, and guarding the keys, users, and devices connected to it.
Common Ways These Risks Show Up
Most hidden security issues follow patterns that repeat across many industries and devices. They may start with careless user behavior, weak internal controls, or software that has not been patched for months. In some cases, the problem begins with an email that looks real, a fake login page, or a mobile app asking for too many permissions. In other cases, the threat is deeper and involves poor cloud settings, exposed databases, or internal misuse of sensitive data. Common warning signs and related highlights include:
- weak passwords reused across multiple accounts
- outdated software with known security flaws
- poor encryption key storage or careless key sharing
- unprotected public Wi-Fi use for sensitive work
- suspicious login attempts from unknown locations
- hidden malware running quietly in the background
- employee mistakes caused by lack of training
- unsecured backups or cloud storage settings
Who Is Most at Risk and Why
The truth is that almost anyone can be affected, but some groups face more exposure than others. Small businesses are common targets because they often have valuable customer data but limited security resources. Large organizations are also attractive because they hold massive amounts of private information and rely on many connected systems at once. Remote workers face extra risk when they use personal devices, weak home routers, or public internet access for business tasks. Regular consumers are not safe either, especially when they save passwords in unsafe places, ignore software updates, or trust every message that appears urgent. The broader lesson is simple: hidden online threats do not only target experts or big companies. They often hit the people and systems that assume they are too small to matter.
ALSO READ THIS :- How Cindy Deangelis Grossman Supported Herschel Walker Through His Rise to Fame
How to Lower the Risk in Daily Digital Life
The good news is that many hidden risks can be reduced with steady habits instead of extreme technical skill. Strong password management, two-factor login protection, software updates, secure backups, and careful handling of private files all make a real difference. People should also pay attention to how data moves between devices, apps, cloud platforms, and email accounts, because exposure often happens during transfer rather than storage. Businesses need clear access rules, regular audits, staff training, and a plan for how to respond when something looks wrong. Even basic steps, if done consistently, can stop a small weakness from turning into a major breach. Digital safety is often less about one perfect tool and more about many smart habits working together every day.
Why Awareness Matters More Than Panic
One of the biggest mistakes people make is thinking that cybersecurity only belongs to technical teams. In reality, awareness is often the first and strongest layer of protection. A careful employee who questions a fake message can stop an attack before it begins. A parent who updates a home router can prevent strangers from using an open network. A student who notices a suspicious login alert can save personal files, payment data, and account access in minutes. Fear does not help much on its own, but awareness does. The purpose of learning about these risks is not to panic. It is to understand that digital threats can be hidden, layered, and patient, which means people need to be calm, alert, and consistent in how they protect their online lives.
Final Thoughts
Fkstrcghtc can be understood as a useful way to describe the hidden side of digital danger, especially where encryption risks and quiet system weaknesses meet. It highlights a truth that many people ignore until something goes wrong: the most harmful online threats are often the ones that stay unnoticed while trust remains high. Whether the issue begins with weak access control, poor data protection, unsafe user habits, or silent malware, the result can be serious if nobody acts early. The best response is not blind trust in technology or constant fear of the internet. It is informed action, stronger habits, regular updates, and a clear understanding that privacy and digital safety depend on both tools and human choices.
FAQs
1. What is Fkstrcghtc in simple terms?
It is a way to describe hidden digital risk, especially security problems that are not obvious at first. It often relates to quiet system weakness, data protection issues, and online threats that stay unnoticed until damage has already started.
2. Is Fkstrcghtc the same as malware?
No, it is broader than malware. Malware can be one part of the problem, but the term also covers weak encryption, risky user behavior, hidden access points, and other silent dangers inside digital systems.
3. Why are encryption risks important?
Encryption protects private data, but it only works well when it is used properly. If the method is old, the keys are poorly stored, or attackers gain account access, private information can still be exposed even when encryption exists.
4. Can regular internet users be affected by these threats?
Yes, very easily. Everyday users can face account theft, payment fraud, device compromise, or privacy loss if they ignore updates, reuse passwords, or trust suspicious messages and websites.
5. What is the best first step to stay safer online?
Start with strong passwords and two-factor authentication on important accounts. After that, keep devices updated, avoid unknown links, and back up important files so one mistake does not cause lasting damage.
6. Do small businesses need to worry about hidden digital threats?
Absolutely. Small businesses are often targeted because they may have valuable customer records but fewer security controls. Even a basic protection plan, staff awareness, and regular checks can greatly lower the chance of a serious problem.
FOR MORE CONTENT: CLOCKMAGAZINE